Introducing tiered storage for Spanner
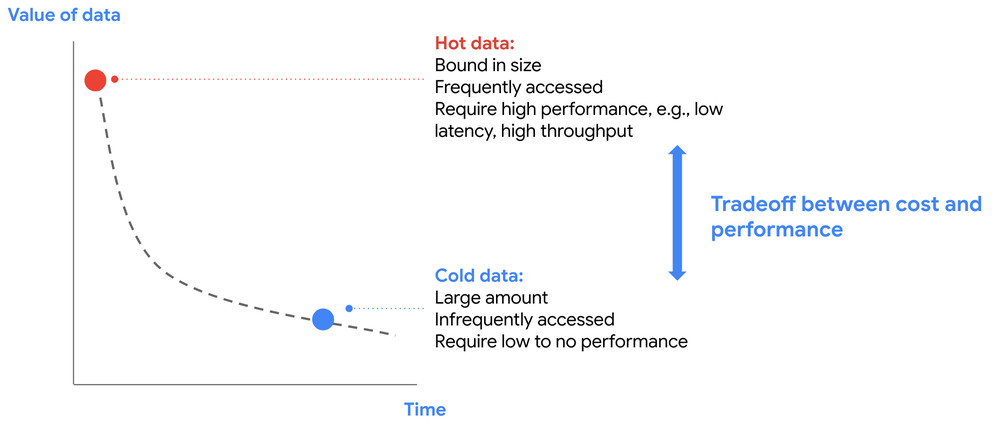
Today, we are excited to announce fully managed tiered storage for Spanner, a new capability that lets you use larger datasets with Spanner by striking the right balance between cost and performance, while minimizing operational overhead through a simple, easy-to-use, interface. Spanner powers mission-critical operational applications at organizations in financial services, retail, gaming, and many […]
Introducing tiered storage for Spanner Read More »