Introducing the new Google Cloud Trace Explorer
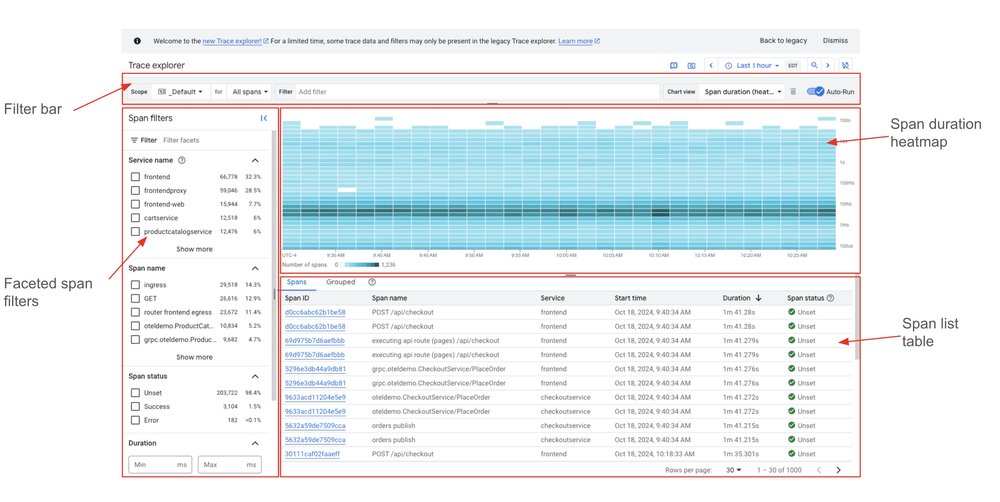
Distributed tracing is a critical part of an observability stack, letting you troubleshoot latency and errors in your applications. Cloud Trace, part of Google Cloud Observability, is Google Cloud’s native tracing product, and we’ve made numerous improvements to the Trace explorer UI on top of a new analytics backend. The new Trace explorer page contains: […]
Introducing the new Google Cloud Trace Explorer Read More »